This post was originally written in early 2020, the pandemic and moving has delayed it. So to has Twitch's slow response to my bug submission.
So Fiona had an issue with her computer and I was trawling around for the answer and found a forum where someone was having the same issue. They'd also posted their full memory.dmp (crash dump online). Turns out it confirmed my suspicion that her wifi card was causing the crash, Dell came out and fixed it, bing bang boom, job done (as I like to say).
But seeing this person's full memory dump got me thinking. Mainly yeesh, that is bad. There are going to be passwords in there, authentication cookies all sorts of things. I wasn't wrong. I've since notified the person I found to delete the file from their 1-drive. But this warning goes out to everyone.
I've done several notifications to vendors and given them the usual 30 days to fix it, so here is my write-up.
First, I tried volatility as I've used it before, but had some big issues with the profile, these are both very recent versions of windows 10, even after updating to 2.6.1 and trying to dump out the memory dump as a raw (I couldn't exactly re-capture it could I). Imageinfo didn't work, neither did dbgscan.
It was when I was looking at the the header of the file to troubleshoot why it wasn't working in hexdump on the test memory.dmp I had from Fiona's computer that I had a though. There is a lot of plain text in here... why hadn't I tried strings.... sure enough pay-dirt.
This got me some interesting results.
$strings memory.dmp |grep -i -A 25 -B 25 google.com
Then just grep for the cookies I know google uses
$strings memory.dmp |grep __Secure >> google.txt
$strings memory.dmp |grep LOGIN_INFO >> google.txt
Fiona's auth tokens, redacted of course.
And I had enough to take over her session and login to youtube, gmail etc. Cool proof of concept I thought. But google times out their sessions every month, so that limits the risk. Lets keep looking. (Nice long strings there too google).
On the original memory.dmp I found, I did the following
$strings memory.dmp |grep ".com"And found the kinds of site the person had been too... among some unsavory data. I found Twitch, gmail etc. No gmail auth tokens which is interesting. I decided to output to a file to read in the built in mate text viewer pluma:
$strings MEMORY-1drive.DMP | grep -i -B 25 -A 25 "twitch" >> twitch.log
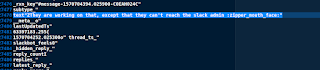
Well isn't that interesting... (redacted obviously). An Oauth token, which you could grab at time of writing and send as a cookie and login.
Yes, I didn't have a twitch account at time of writing, but I have one now with... checks notes 40 followers, ah well.
I reported this to the user and to Twitch, who didn't get back to me. Bugcrowd did, directing me to their reporting page, on which I got no reply.
Also Twitch, short Oauth string, that doesn't seem to time out to quick, you should probably fix that. This memory.dmp had been posted to a forum end of 2019. But still worked in May 2020.
I re-submitted to Twitch's bug-reporting page in 2022, and am awaiting a response.
But I kept looking. The below google searches will find lots of memory.dmp's dating back to 2003, well they did before I alerted the forum owners.
"https://1drv.ms/u/s!" memory.dmp
"https://www.dropbox.com/l/" memory.dmp
"https://drive.google.com/open?id=" memory.dmp
Interestingly box didn't show up much in searches, and they also have the option to timeout shares, so the one I did find didn't work. Good job Box.
"box.com/v/" memory.dmp
Another interesting find when I continued this in 2022 is Slack appears to log all the messages you sent and seemingly received to your memory. But no Oauth tokens, and the images shared in Slack require authentication to the channel.
Further to all this... You can simply fire these memory.dmp's up in WinDbg and pull out Lsass. Yep that is the passwords of the people who used these systems. One seems to work for Vmware or at least uses a lot of their Slacks (who had posted to a forum to get Docker on windows support :), another our Twitch streaming friend.
Oh and Vmware you have some fun emoji's on your slack
https://emoji.slack-edge.com/T0EANJNGH/micdrop/9534194af287fe1c.png